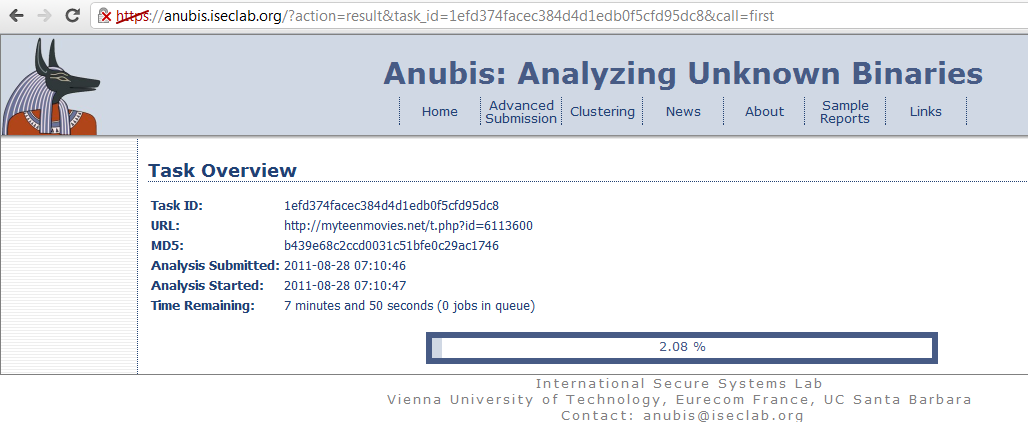
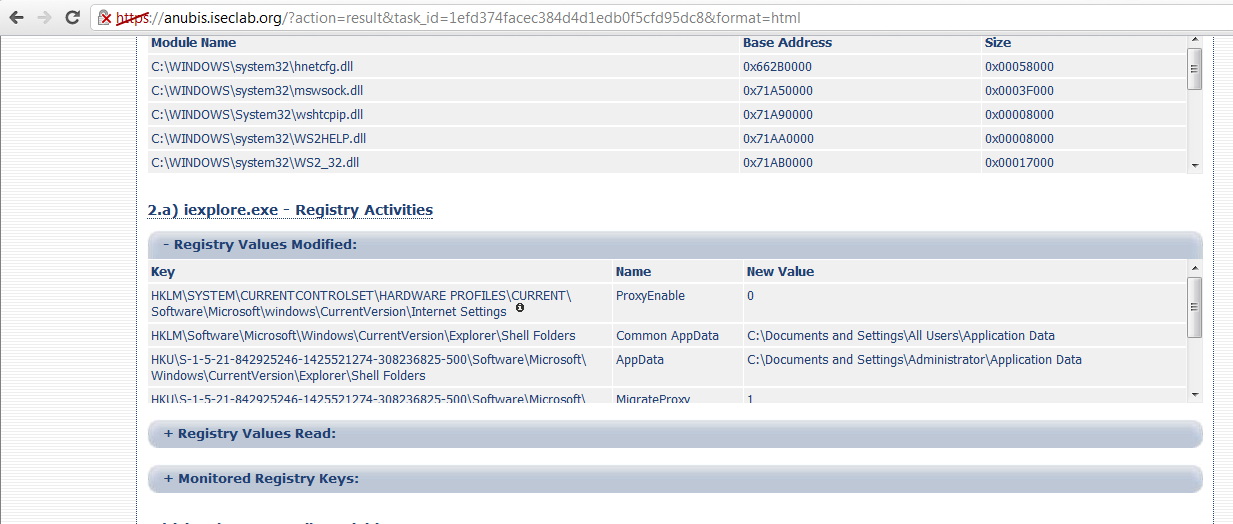
![PDF] Needles in a Haystack: Mining Information from Public Dynamic Analysis Sandboxes for Malware Intelligence | Semantic Scholar PDF] Needles in a Haystack: Mining Information from Public Dynamic Analysis Sandboxes for Malware Intelligence | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e33f910829939417e6273e0e5e6b26887f6e1ce1/17-Table5-1.png)
PDF] Needles in a Haystack: Mining Information from Public Dynamic Analysis Sandboxes for Malware Intelligence | Semantic Scholar

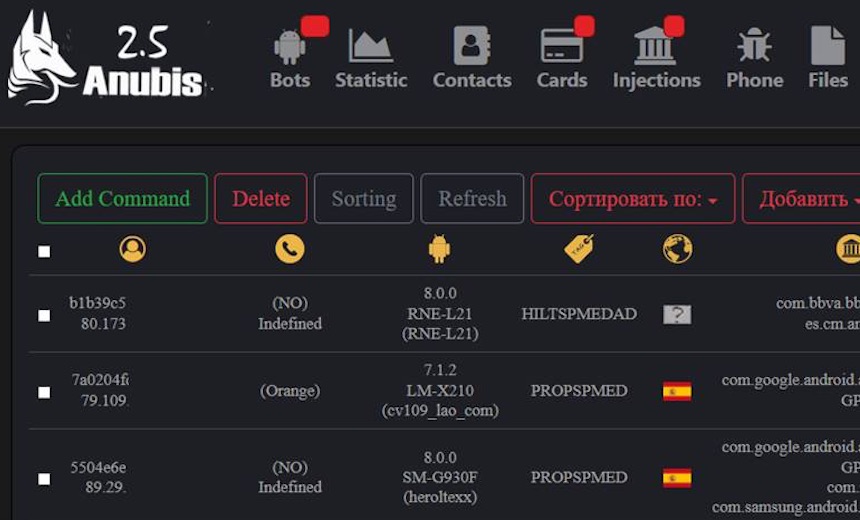
Deep Malware Analysis - Architecture independent Malware Similarity Analysis with Joe Sandbox Class 3.0

StSHS'?!N/vNA/W'/.-i / Egypt :: black :: god :: countries :: horus :: anubis :: art (beautiful pictures) / funny pictures & best jokes: comics, images, video, humor, gif animation - i lol'd

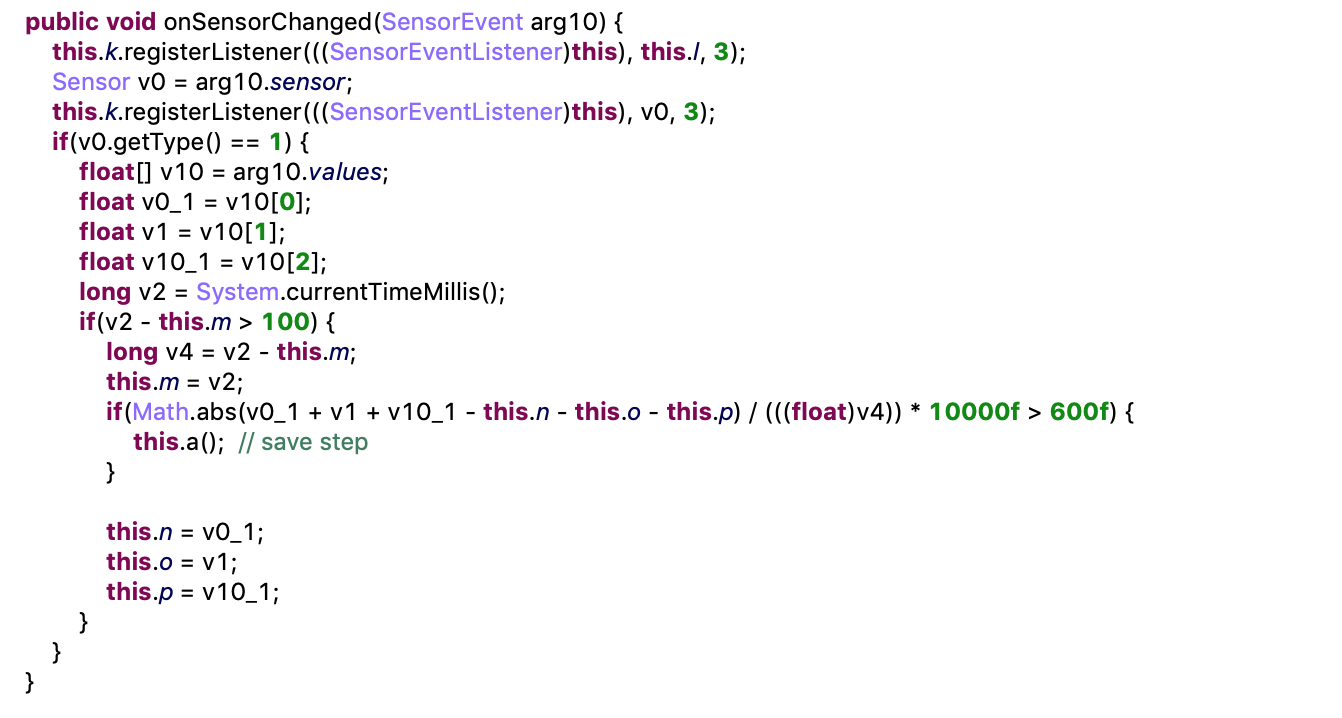
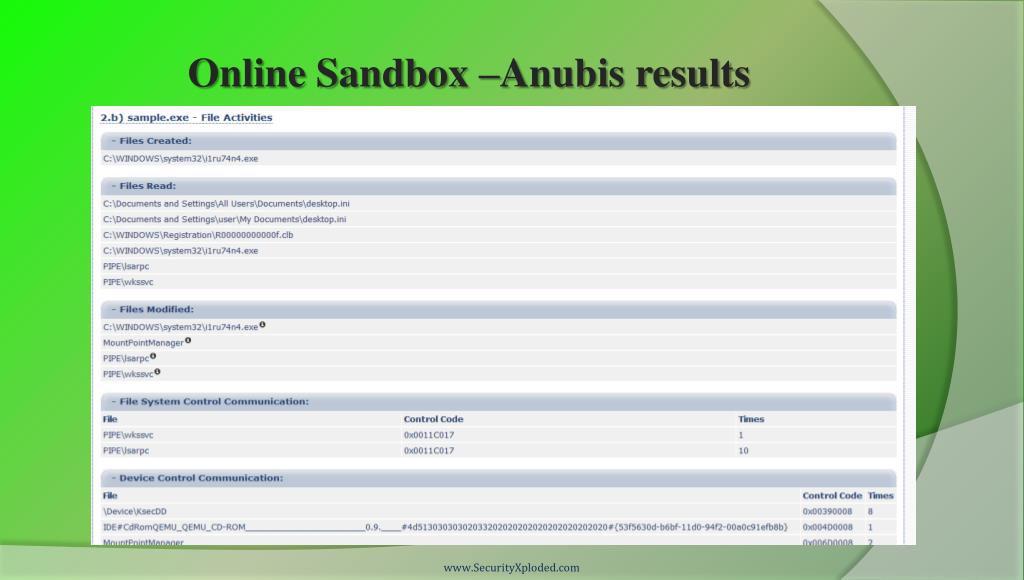
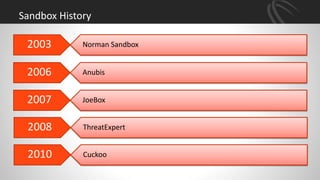
Copyright © 2011, A Behavior-based Methodology for Malware Detection Student: Hsun-Yi Tsai Advisor: Dr. Kuo-Chen Wang 2012/04/ ppt download