Snyk Security - Code, Open Source, Container, IaC Configurations - IntelliJ IDEs Plugin | Marketplace

Figure 6 from Source Code Analysis to Remove Security Vulnerabilities in Java Socket Programs: A Case Study | Semantic Scholar
Snyk Security - Code, Open Source, Container, IaC Configurations - IntelliJ IDEs Plugin | Marketplace



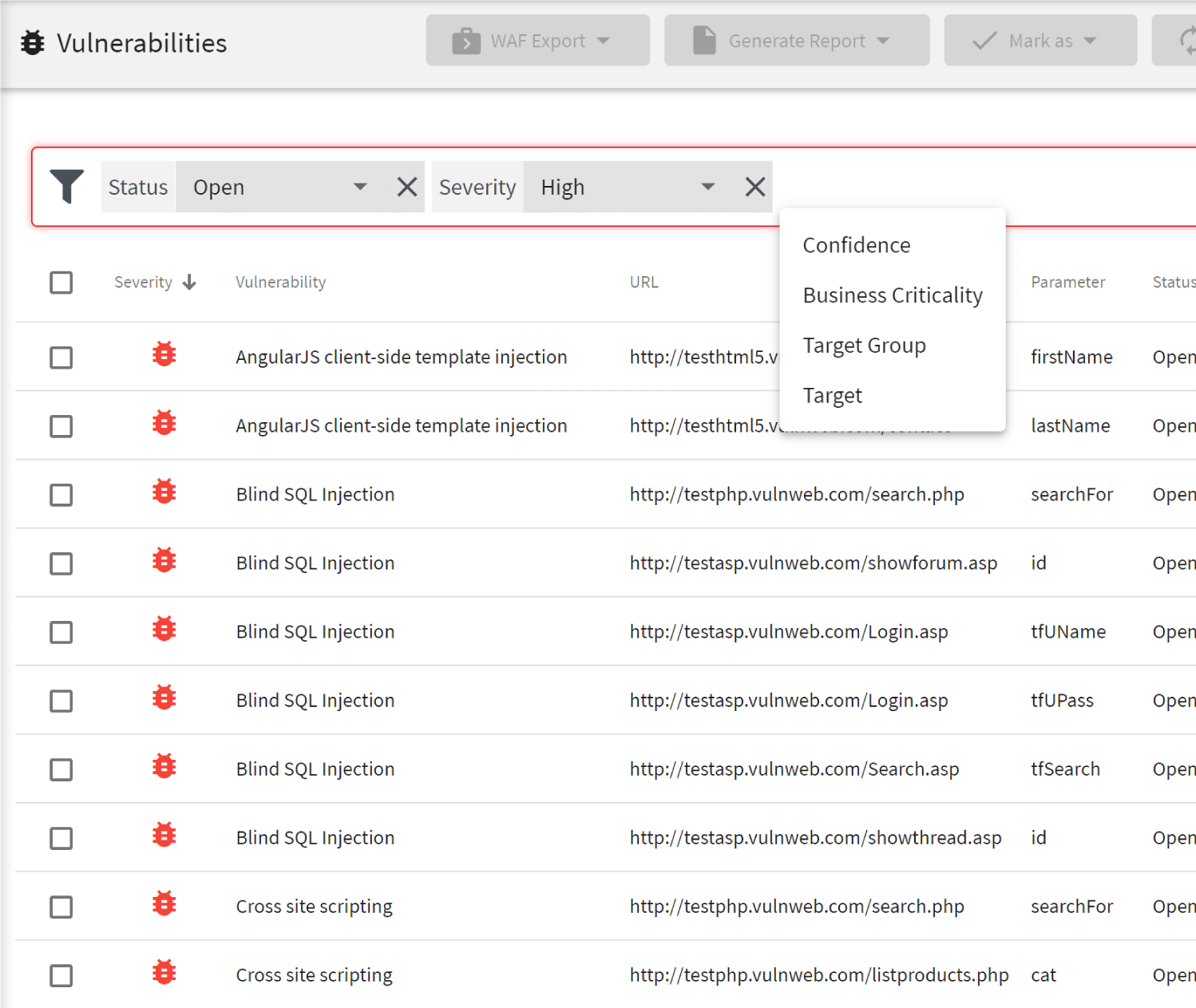
![14 best open-source web application vulnerability scanners [updated for 2020] - Infosec Resources 14 best open-source web application vulnerability scanners [updated for 2020] - Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/2020/10/scanner09242014.jpg)